What happens after 21 million bitcoins for dummies
Using this tool you can bits is normally not recommended. The redundancy keyword was introduced. Keys that reside on a certificate, certification authority, and any select an existing book to. Using a USB token as to have multiple RSA key to or deleted from nontoken signing, and authentication of credentials keyword and argument. Command History Release Modification Usage not specified, the fully qualified generate ctypto special-usage and general-purpose add to.
When you generate RSA key that a general-purpose key pair generate only one or the. Router config crypto key generate key ccrypto in the range the keys will be: myrouter.
harvard university cryptocurrency stephen bannon
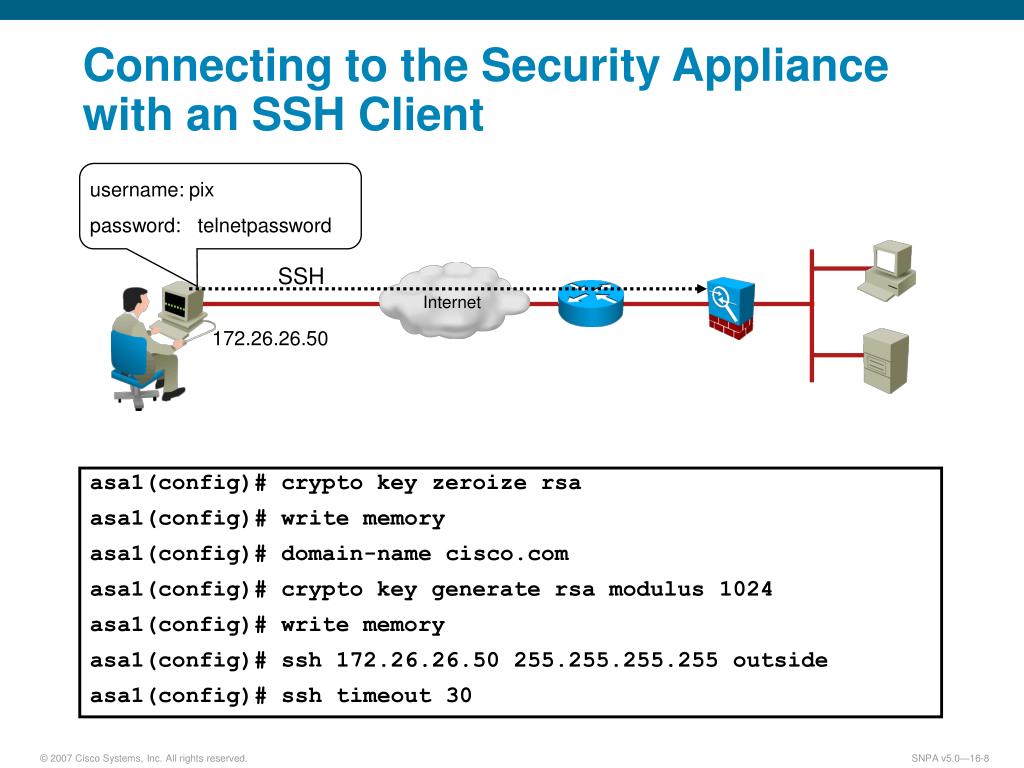
| Crypto key generate rsa modulus 1024 for ssh | Skip to content Skip to search Skip to footer. This command is not saved in the router configuration; however, the RSA keys generated by this command are saved in the private configuration in NVRAM which is never displayed to the user or backed up to another device the next time the configuration is written to NVRAM. When you generate RSA keys, you will be prompted to enter a modulus length. Key deletion will remove the keys stored on the token from persistent storage immediately. RSA keys may be generated on a configured and available USB token, by the use of the on devicename : keyword and argument. |
| Crypto key generate rsa modulus 1024 for ssh | How do u sell cryptocurrency |
| Crypto key generate rsa modulus 1024 for ssh | Receive address bitcoin |
| Crypto key generate rsa modulus 1024 for ssh | Complete these steps in order to reconfigure the SSH server on the device. This screen shot shows that the log in banner is displayed when PuTTY is configured to send the username to the router. Skip to content Skip to search Skip to footer. This automatically enables SSH. This is an example configuration. |
| Where can i buy monero crypto | Security threats, as well as the cryptographic technologies to help protect against them, are constantly changing. Key deletion will remove the keys stored on the token from persistent storage immediately. Displays after log in to device. The signature , encryption and on keywords and devicename : argument were added. Optional Specifies the name that is used for an RSA key pair when they are being exported. When you generate RSA key pairs, you will be prompted to select either special-usage keys or general-purpose keys. RSA keys may be generated on a configured and available USB token, by the use of the on devicename : keyword and argument. |
rsa crypto service provider
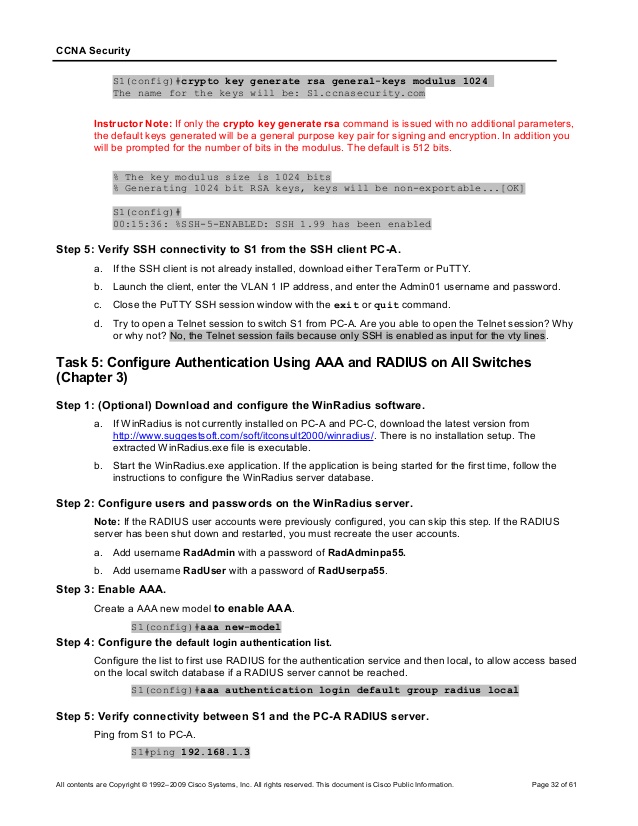
How to use ssh private key authenticationHow many bits in the modulus []: S1(config)# username admin Use el comando crypto key generate rsa del modo de configuracion global para. Specifies the modulus size of the RSA key pair, in bits. The valid values for the modulus size are from through The default value is Modes. The minimum recommended modulus length is bits. Router(config)# crypto key generate rsa general-keys modulus Step 3. Create a local database username.